
Protecting Canadian Organizations Against Business Email Fraud: Strategies and Best Practices
By Julie Jeffries, Microsoft
News microsoft
Sponsored by Microsoft
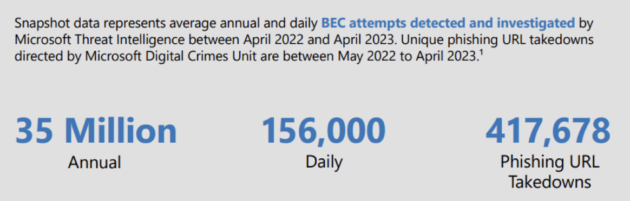
Business Email Compromise (BEC), also known as email account compromise or email fraud more broadly, is one of the most financially damaging online crimes. This email-based cyberattack poses a significant threat to Canadian business. Troublingly, it’s on the rise. Between 2019 and 2022, Microsoft’s Digital Crimes Unit observed a 38% increase in Cybercrime-as-a-Service targeting business email. Driving this surge in attacks is an increase in sophistication and the introduction of new threat tactics that make BEC more difficult to identify and block. Understanding the BEC threats and the proactive steps that organizations can take to prevent an incident can help businesses stay ahead of the cyber bad actors.
Evolving Tactics
The latest Microsoft Threat Intelligence Cyber Signals Report identifies several new key risks causing the recent surge in BEC. Among them, threat actors are now leveraging residential internet protocol (IP) addresses to make campaigns appear locally generated. This new tactic allows cybercriminals to circumvent “impossible travel” alerts intended to block malicious entry.
Microsoft has also observed an increase in the use of platforms like BulletProftLink, a large-scale Cybercrime-as-a-Service operation which offers phishing kits, email templates, hosting and automatic services at a relatively low cost. By utilizing Internet Computer public blockchain nodes to host phishing and BEC sites, BulletProofLink offers a sophisticated decentralized web offering that’s difficult to disrupt.
The Impact of BEC Attacks
Successful BEC attacks cost organizations hundreds of millions of dollars annually. In 2022, the FBI reported more than 21,000 complaints of Business Email Compromise with adjusted losses over 2.7 billion. In the same year, the IC3 Recovery Asset Team (RAT) initiated the Financial Fraud Kill Chain on 2,838 BEC complaints involving domestic transactions with potential losses of over $590 million.
While the financial implications of successful attacks are significant, BEC also carries potential long-term damage including identity theft and loss of confidential data or intellectual property. Both can cause irreparable reputational damage.
Defending Against BEC Attacks
Defending against BEC requires both vigilance and awareness. Organizations with fully remote or hybrid workforces must take special precaution to ensure employees are prepared to identify and manage email threats amongst the high volume of emails received every day.
Here are steps organizations can take to enhance their security posture:
- Configure email systems to flag messages from external parties, enable notifications for unverified senders, and block unconfirmed identities, reporting them as phishing or spam.
- Enhance email security with multifactor authentication (MFA) that requires additional verification (code, PIN, or fingerprint) along with a password. Passwordless technology adds further security by verifying identities on the device, reducing vulnerability during online connection.
- Educate employees on spotting fraudulent emails, like domain and email address mismatches, and the risks and costs of successful BEC attacks. Encourage employees to verify financial transactions through direct phone conversations to prevent fraud. Establish clear policies emphasizing the importance of contacting individuals or organizations directly instead of relying solely on suspect messages.
- Use AI-powered secure email solutions for stronger defense against BEC attacks. These platforms offer advanced phishing protection, suspicious forwarding detection, and centralized security policy management. Cloud-based email and productivity apps provide continuous software updates for added security.
- Implement Zero Trust principles and automated identity governance to control application and data access, hindering cybercriminals from moving within the network.
- Shift to a secure payment platform with authentication mechanisms to reduce the risk of unauthorized payment transfers and ensure legitimate transactions.
Effectively addressing and mitigating the risks of Business Email Compromise requires a cross-functional approach, involving executives, finance employees, human resource managers, IT professionals, compliance officers, and cyber risk officers. Businesses that fail to create a culture of security risk leaving crucial gaps for threat actors to exploit. Microsoft is committed to working with security executives to build strong cybersecurity postures that pre-empt new and emerging threats, building a safer future for Canadian businesses.
To learn more, read the Microsoft Threat Intelligence Cyber Signals Report.
To get started on implementing Zero Trust Principals, access Microsoft’s comprehensive playbook for Zero Trust Security Strategy.
Print this page
Advertisement
- Global Affairs Canada issues LGBTQ+ travel advisory for United States
- Border infrastructure bolstered as Ottawa reviews response to Emergencies Act inquiry
Leave a Reply