
How to prevent insider risk within a company
Alanna Fairey
Features Public Sector Security Check Point carleton university chelsea manning Edward Snowden FortiGuard Labs Insider riskInsider risks are sometimes perpetrated innocently by employees, but there are remedies that can limit an organization’s exposure
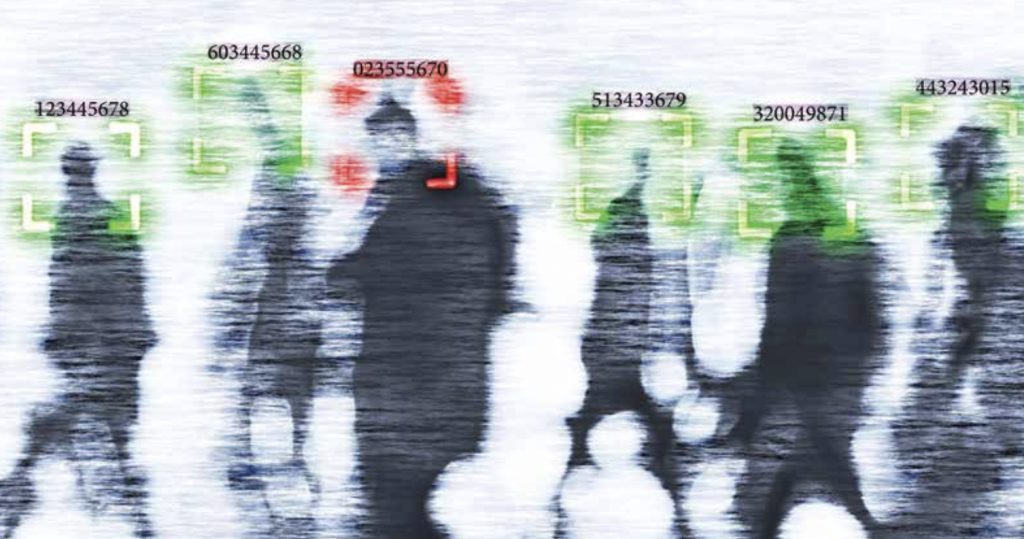 Image: andreusK / iStock / Getty Images Plus
Image: andreusK / iStock / Getty Images Plus While there have been many examples over the years of disgruntled or malicious workers intentionally subverting the confidentiality and integrity of their companies, some employees may be doing harm without even realizing it.
Lina Tsakiris, a security professional who currently works with one of Canada’s major financial institutions explains that an insider risk — whether malicious or non-malicious — commits an untoward action that could negatively impact the organization from either a financial, reputational or operational impact.
“While it’s typically perpetrated by proprietary employees, contractors, third- and fourth-party suppliers are also considered insiders as well,” Tsakiris says. “When external threat events have internal impact, such as malware, this is also considered an insider risk-related threat.”
Well-known security compromises, such as those carried out by Edward Snowden and Chelsea Manning, have highlighted a much wider issue of insider threats.
“Unfortunately, when a compromise occurs, it could become front page news and it can damage the reputation of the affected organization,” says Victor Munro, security industry expert and PhD student at Carleton University’s Norman Paterson School of International Affairs. “Accidental insider threats are occurring all the time, and these are threats that are coming from well-intentioned, non- malicious employees.”
It does not take a great deal of sophistication to send an employee a realistic looking email or text, prompting them to provide sensitive information or access to the network. According to Derek Manky, chief of security insights, global threat alliances, FortiGuard Labs, cybercriminals attempt to trick employees to get access.
“The most common tactic used is phishing, which are cleverly disguised communications that appear to come from a trusted source asking victims to share information or download a malicious file,” Manky says. “We even see adversaries creating fake social media profiles to befriend victims while posing as a current or former co- worker, job recruiter, or someone with a shared interest.
“Their goal is to trick the victim into providing sensitive information or downloading malware to their device.” Employees can also unwittingly become insider risks in a moment of innocent forgetfulness. Tsakiris says that something as simple as an employee not locking a work computer screen when walking away from their desk can also leave them susceptible.
“Having a mindful approach to good security hygiene practices is important to mitigate insider risk,” Tsakiris stresses.
With employees working remotely because of the COVID-19 pandemic, they are more susceptible to becoming an insider risk, especially if they are working with a personal laptop.
“With so many more people working from home and perhaps unable to quickly check with someone on the veracity of an email or file sent to them, people are more susceptible,” Manky explains. “Our FortiGuard Labs research shows criminals understand this, which is why we’ve seen a surge in these kinds of attacks since the onset of the pandemic.”
Unfortunately, a small error on the part of an employee can have huge consequences for the organization that they work for.
Manky explains that for an employee, unknowingly becoming an insider risk may mean compromised personal data, such as banking information. “For their employers, it can give criminals access to sensitive data or provide the basis for a ransomware attack, leaving the company unable to function the way it needs until they meet the financial or other demands of attackers,” Manky says.
Culture of prevention
Increasingly, the accountability is being shifted away from employees and more towards security and IT professionals to adequately equip them to deal with these issues and understand what the implications are.
Reviewing the reasons for the shift, there are two issues that stick out in Manky’s mind.
“Ultimately, security professionals are tasked with ensuring adequate levels of security and protection across the organization and of course they have a great deal of responsibility in preventing attacks,” Manky says. “However, we also know that there’s a chronic, global shortage of cybersecurity professionals and Canada is no exception. Security teams often find themselves stretched or under resourced as a result.”
The second issue, according to Manky, is that even the best-trained security professionals cannot overcome outdated technology. “There are risks that come with using aging security solutions or networks that don’t take advantage of the latest technology, including things like AI to provide automation and real time monitoring that reduces the pressure on IT teams,” he says.
However, Manky says that assigning blame in the workplace is not productive. “It is better to focus on a cohesive strategy to combat social engineering,” he says.
To educate employees on how to better protect their information and avoid becoming an insider risk, Tsakiris stresses the importance of creating a culture of prevention, which she says applies to everything security professionals do.
“It’s a continued philosophy of what we believe as security practitioners,” Tsakiris says. “We leverage our employees to be our ears and eyes as we cannot be everywhere at all times. We use all available conduits to report suspicious activity and behaviour.”
Tsakiris adds that she is seeing more insider risk initiatives in the private sector as a way to formalize a program within the corporate security or IT department.
Continuing the theme of maintaining good security hygiene practices, Manky says that companies should get the basics right and implement or refresh their training.
“It’s critical that people know what they need to do and how to spot fraudulent communications,” Manky stresses. “It doesn’t have to be hard or expensive,” he says, adding that Fortinet offers a free NSE Institute to help educate workers on the threat landscape.
Employers are also encouraged to have their employees take a look at all the devices they use — including those they own and use when working from home — and ensure they are patched and up to date.
“Now is also the perfect time to reinforce basic password best practices too,” Manky says.
Better together
Ultimately, to prevent further incidents of accidental insider risks, an organization must create an environment with a strong foundation in security, according to Tsakiris.
“Good security hygiene includes creating a culture of prevention, providing the right level of training and awareness so employees understand what untoward activity may look like in the in the workplace,” Tsakiris says. “Employers need to help employees by giving them the appropriate reporting conduits to be able to escalate any concerns that they may have.”
With more industry initiatives emerging, such as Insider Threat Awareness Month in September, Munro says that this is a step in the right direction. “These are positive things because they’re heightening the potential seriousness of the issue to corporate culture,” Munro says.
“Whether public or private, insider risk is an issue and, at the very least, we should be talking about it.”
While there has been a call to security and IT professionals to ensure that employees are protecting their information, it is imperative that all levels of an organization are better educated on security measures.
In Manky’s view, senior staff must set an example for their employees.
“Often, IT teams are left to carry the security message alone and there is a risk that the message gets lost amid other day- to-day priorities and the seriousness of the issue is not conveyed,” Manky says.
“Make senior leaders — not just IT — the vocal champions of cybersecurity, reminding employees in clear communications that cyber hygiene is critical to the successful operation of the business and an expected part of everyone’s job description.”
Print this page
Advertisement
- US still unraveling ‘sophisticated’ hack of nine government agencies
- Stricter public health measures now in effect at Canadian borders, airports
Leave a Reply