
Webinar: How to minimize insider risk within an organization
Alanna Fairey
News Canadian Water and Wastewater Association Central Intelligence Agency (CIA) Insider risk National Security Agency (NSA) public safety canada Regional Municipality of Durham Sandhurst Consulting Water Canada Window on WaterThe first of a four-part series, the webinar focused on how to prevent insider risks
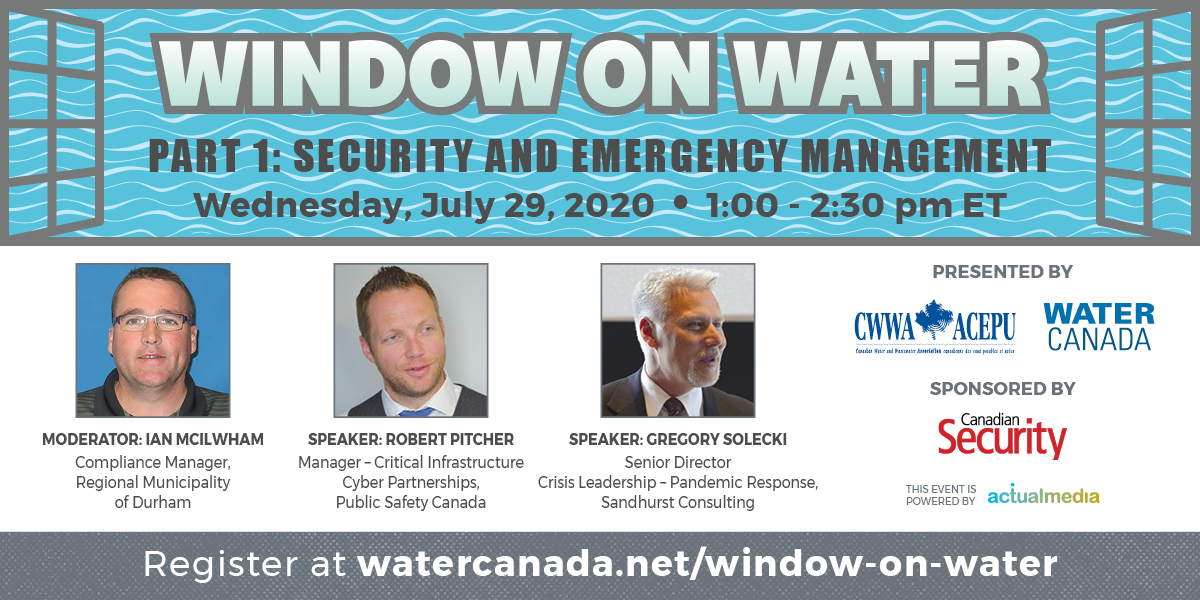
On July 29, Water Canada presented “Window on Water,” a webinar on security and emergency management with a focus on insider risk. Canadian Security magazine was the media sponsor for the presentation.
The first of a four-part series, the webinar was moderated by Ian Mcilwham, who is the compliance manager at the Regional Municipality of Durham, and chair of the Canadian Water and Wastewater Association’s (CWWA) Security and Emergency Committee.
Speakers included Robert Pitcher, manager of critical infrastructure partnerships at Public Safety Canada and Gregory Solecki, director of crisis leadership — pandemic response at Sandhurst Consulting.
Insider risk relates to people working within an organization to subvert the confidentiality, integrity, and availability of the information contained within the walls of that entity.
In his presentation, Pitcher used his platform to use real-life examples of insider risks and provided insight into what organizations should do to minimize the risk.
“No organization is certainly an island,” Pitcher said in his presentation. “What’s important is to understand what your key assets and systems are, know your partners and know your risk.”
Pitcher used the example of the 1984 Bhopal gas tragedy, a gas leak incident at a pesticide plant that claimed the lives of an estimated 16,000 people. The cause of the disaster remains under debate, but there was speculation and accusations that a disgruntled employee took the fire hose and plugged it in to the tank causing the explosion.
” I like to use the [Bhopal gas tragedy] example because it’s an example of the negative effects that one person could potentially have to any organization,” Pitcher said. “Hundreds of thousands of people suffered the effects of that for many years in common or still suffer from it.”
Pitcher went on to explain that organizations need the principle of least privilege and separation of duties for critical systems and data.
“If somebody has access to a part of the organization, make sure it’s something that fits within their roles and responsibilities,” Pitcher advised.

Having protocols when employees unleash threats is imperative for organizations, says Pitcher
Establishing protocols to report, track and respond to unusual incidents will also minimize insider risk, according to Pitcher, citing the examples of the 2015 Charlie Hebdo attacks and 2019 Aurora, Ill. warehouse shootings. In both cases, the perpetrators had previously made threats to kill, but the comments were never reported to management.
“This stuff should be reported, especially in these times,” Pitcher said. “It should be tracked and there should be a way to identify and act on comments like that.”
Pitcher also advised organizations to consider engaging security intelligence, if they suspect something dangerous could happen at the hands of an insider.
Finally, Pitcher looked at the case of whistleblower Edward Snowden, who copied and leaked highly classified information from the National Security Agency (NSA) in 2013 when he was a Central Intelligence Agency (CIA) employee and subcontractor.
“[Snowden] took out gigabytes of information, and this should have been tracked on the system,” Pitcher said. “He was also accessing personal system that he shouldn’t have able to access, so track this information, and then make sure your organizations take action against it.”
Pitcher’s other piece of advice in the case of Snowden is to limit or restrict portable storage devices, as he noted that Snowden was able to put all of the information on a USB and walk out the door with it.
Pitcher concluded his presentation by stressing the importance of promoting a culture of security at any given organization.
“There is always a level of increasing your security, I would say the 100 per cent solution, doesn’t exist, but I think you can apply a lot basic cyber security physical security procedures to help elevate your level of security.
“Part of that is raising awareness of the threats, both from the outside, and from within,” said Pitcher.
Print this page
Advertisement
- Toronto, Peel to join Stage 3 of reopening Friday; Windsor Essex left behind
- Q&A: Keith Melo, manager of security & life safety, CF Fairview Mall