
Photo ID card gets facelift, but more responsibilities
By Rosie Lombardi
News Data Security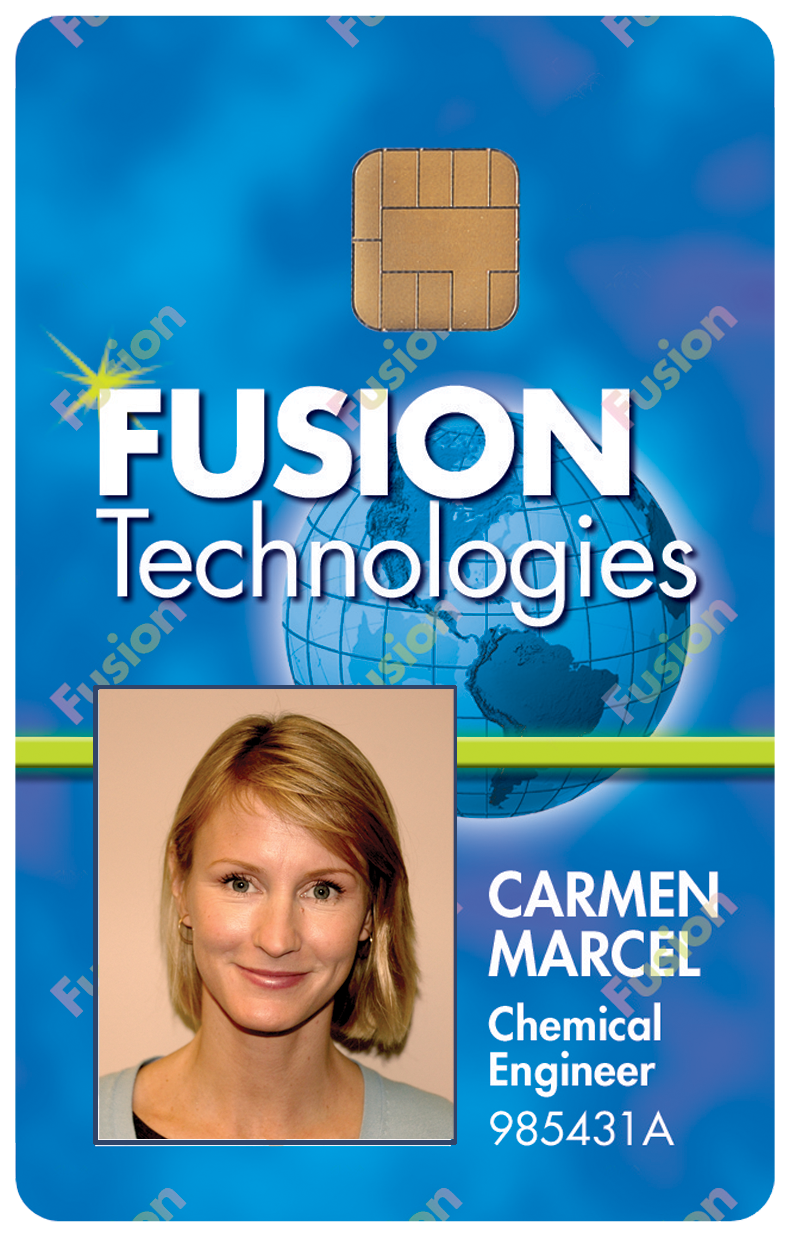 The ubiquitous photo ID card is undergoing some changes. Some of these are cosmetic but some are deeper. Many organizations are rethinking the information placed on employee cards and extending their use into new areas.
The ubiquitous photo ID card is undergoing some changes. Some of these are cosmetic but some are deeper. Many organizations are rethinking the information placed on employee cards and extending their use into new areas.
Displaying the company name and logo has been the standard for many
years, but many organizations are starting to move away from this so
lost badges can’t be immediately associated with the company, says Adam
Ely, security director at TiVo, a San Francisco-based provider of advanced television services.
Some companies are particularly open to risk, as they even place the
company’s address on the back to enable a finder to return a lost card.
If it falls into the wrong hands, this may provide an incentive to go to
the office and try the card.
“We stress that companies should get a PO mail box and put that instead
on the card,” says Peter Alexander, security compliance manager at CB
Richard Ellis Global Corporate Services, a property management firm
based in Markham, Ont.
Companies in higher-risk sectors, such as aerospace, government,
software and health care, are starting to move away from placing the
employee’s last name on the card, as a person’s full name can be easily
Googled to find the company name, and other personal information can be
found on LinkedIn and other sites online.
“Many organizations just place the first name and photo without the
company name or even the employee’s last name. There’s really no good
reason to put the last name, as security guards check by associating
faces with the photo on the credential,” says Jeff Sharpe, president of
Avon Security Products, based in Concord, Ont.
Some companies are going even further and dropping employee names
entirely, says Ely. “Companies such as Microsoft are now beginning to
use different coloured IDs to distinguish if employees are full-time
staff, contractors, or vendors, with a photo but no name or company
detail.”
However, some companies like to display their logo on the card, says
Sharpe. “It’s a corporate cultural thing, as it signals membership to
their club. Most of the brokerage and law firms on Bay Street in Toronto
put everything on the card. But they impress on their employees that
they must call right away if they’re lost so they can kill the card.”
Another big trend is using the reverse side of the card to place
emergency information to maximize its usefulness to the employee for
purposes beyond identification.
“Companies will place phone numbers to call for after-hours emergencies,
fire, and so on. They’re moving away from thinking about badges as only
credentials and realizing that it’s a piece of information they have on
their person at all times on-site,” says Ryan Park, senior product
manager at HID Global Corp., a security card provider based in Irvine,
Calif.
Card printers
Magnetic stripe technology for ID badges has been around for almost 15 years, so the costs have gone down considerably over the years. “Card printers are affordable, so even low-volume organizations are finding it inexpensive to do it in-house by security administrators,” says Alexander.
But the downside is that this creates a new risk. Since these printers are widely available, counterfeit badges can be easily made. “Organizations need to have controls around access to these printers within their organizations. They need to take precautions to keep the printer, software and blank badge stock locked up. Most companies are pretty good at maintaining these controls,” says Alexander.
While in-house controls may be good, there are still external criminal elements to tackle. “We’re seeing more fraud than ever, with websites offering various fake IDs, often to support terrorist activity. There’s a lot of older equipment out there that can be easily bought on the web, so the challenge is to create uniqueness in new ID card products to ensure we’re adding security to the entire issuance system,” says Park.
HID has added extra layers of security to the process to safeguard it end-to-end, he adds. “We use password protection for our consumables and our equipment, so if people send a print job we can authenticate the materials being used are correct. And we’re also adding features such as ultra-violet (UV) printing, which generates images on the card that can only be seen under UV light. So you can only use the equipment if you have the correct system in place, and you can’t use the blank stock with older products.”
Next-generation issues
The newer RFID technology in contactless cards makes them more secure than magnetic stripe cards, says Park. “Magnetic stripe cards are pretty open to fraud, as skimmers can easily take the data off, versus contactless cards, which have data encryption, secure connections to card readers, and so on.”
Nevertheless, Park guesstimates about 70 per cent of cards issued today still are magnetic stripe, as many organizations already have this infrastructure in place. “But there are systems available that offer reading capabilities for both types of card on one reader, so companies with multiple locations can do a staged transition over time.”
Magnetic stripes are on their way out, agrees Alexander. “Many companies use multiple access cards because they don’t have one solution across their business. Some who lease their office sites will piggyback off the landlord’s card system. I’ve seen security managers with pocketfuls of cards for all the locations they’re responsible for. Companies in this scenario should look for one enterprise-wide solution to get it down to one card.”
Merging physical access to the building and logical access to the employee’s computer on one card, would be ideal.
“Employees can use the card to access the front door, then use it to log onto their computers. It’s dual authentication, as they need to both enter their passwords and present the card. So the logic used to access the building is the same for computers,” says Park.
Microsoft provides software that supports contact and contactless cards, and Dell recently entered into a partnership with HID to embed readers in their hardware, he adds. Computers without embedded readers or software can use a USB port to connect an external card reader.
This is the next evolution in card technology, says Dan Griffin, a software security consultant at Seattle-based JWSecure Inc. “Physical and logical systems don’t talk to each other today but they should. Tying them together can prevent breaches. For example, if the physical log says an individual isn’t in the building, are there certain systems that account shouldn’t have access to at that time?”
Rosie Lombardi is a Toronto-based freelance writer.
Print this page
Advertisement
- Air cargo security program aims to improve safety, but at what price?
- Contemporary’s special treatment
Leave a Reply