View As Webpage | View Archives
MMMM d, yyyy |
||
| FEATURED NEWS: Six types of cyber criminals defined | ||
| If you click the images or links in the Sponsor Spotlight advertisement we will provide your subscription contact information only to that sponsor. | ||
 | ||
News | ||
Guidance about anti-terrorism laws remains secretThe federal government’s directions to Canada's spy agency about using contentious new anti-terrorism laws won't be made public >> Read full article |
||
Airport wants fingerprint check of Uber driversA battle is brewing in Atlanta over background checks for drivers with Uber, Lyft and other ride-booking firms >> Read full article |
||
Suspect arrested on fear of terrorism, RCMP sayPolice arrested Kevin Omar Mohamed under a little-used section of the Criminal Code which allows authorities to detain someone who might commit a terrorist act >> Read full article |
||
 | ||
Sponsor’s Message | ||
Complimentary Webinar by IBMAs our online world evolves, network endpoints—which include desktops, mobile devices, servers and kiosks—are proliferating at a rapid pace, making organizations increasingly vulnerable to cyber threats. Traditional security solutions — such as anti-virus and anti-spyware software—can’t keep up, and no longer offer sufficient 24/7 protection against today’s sophisticated cybercriminals. | ||
Featured News | ||
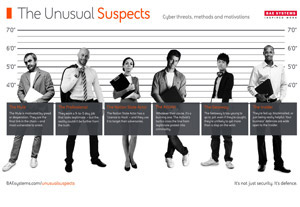 Six types of cyber criminals definedThreat intelligence experts at BAE Systems have profiled six prominent types of cyber criminals and exposed how they can cause harm to businesses. The intention of the company’s information campaign is to help enterprises understand the various enemies they face so they can better defend against cyber attacks. “The Unusual Suspects” is based on research that uncovers the motivations and methods of the most common types of cyber criminals. These include the mule, the activist and the insider. >> Learn More… | ||
 | ||
NEWS | ||
Several agencies use new information-sharing rulesAt least four federal agencies have used the controversial information-sharing powers that are part of the omnibus security bill known as C-51 >> Read full article |
||
Civil rights groups question use of Stingray device by policeA legal advocacy organization has filed an appeal with the B.C. privacy commissioner after Vancouver police refused to confirm they use a mass-surveillance device >> Read full article |
||
Hudson’s Bay Company agrees to educate staff about racial profilingThe retailer has settled a discrimination complaint related to a security guard questioning a 77-year-old African Canadian woman about her purchase of a rug >> Read full article |
||
Event Calendar | ||
ISC WestLocation: Las Vegas, Nev. |
||
Border Security ExpoLocation: San Antonio, Tex.. |
||
Security Canada EastLocation: Sheraton Laval, Laval, QC |
||
ASIS Toronto Chapter 23rd Annual Best Practices SeminarLocation: Markham Event Centre |
||
Security Canada AlbertaLocation: River Cree Resort & Casino, Edmonton, Alberta |
||
Tracking Terrorism Symposium: Countering the Threat of Violent ExtremismLocation: Oshawa, Ont. |
||
Port SecureLocation: Toronto, Ont. |
||
The World Conference on Disaster Management (WCDM)Location: Mississauga, Ont. |
||
Focus On DronesLocation: Richmond Hill, Ont. |
||
|
Privacy | Unsubscribe
Copyright ©yyyy Annex Business Media P.O. Box 530, 105 Donly Drive S, Simcoe, ON, CANADA N3Y 4N5 |








